Resume Formats That Help Get You Job Interviews
Find out how to choose the best resume format to showcase your skills, experience, and achievements.
Free Resume Templates Optimize your resume
-
Trusted by:
-
-
-
-
-
A good resume format organizes your skills, experience, and achievements. It tells hiring managers what they need to know.
Having a good resume format is important for another reason. It helps applicant tracking systems (ATS) read and understand your resume.
ATS is a computer software that most companies use today to help them hire employees. One of the main jobs of ATS is to screen the hundreds of resumes that come in for every job opening.
If your resume isn’t formatted the right way, the ATS will have trouble reading it. This makes it far less likely that a hiring manager will see your resume.
Don’t worry! Choosing a resume format isn’t as hard as it sounds. This article will guide you through the process.
By the end of it, you’ll know which resume format is best for your situation.
The 3 basic resume formats
There are three basic resume formats to choose from. They are:
- Chronological – Lists your work history in order, starting with your most recent job first.
- Functional – Focuses on your skills and accomplishments instead of your work history.
- Hybrid – Places your skills and accomplishments at the top, before your work history.
It’s important to understand the pros and cons of each format. This allows you to choose the one that best suits your specific situation and career goals.
After choosing a format, consider using a resume template to help create your resume. A template is a pre-designed layout that provides a structured framework for presenting your skills and experience. All you have to do is fill in your information.
Jobscan has a variety of free resume templates you can use. Our templates come in all three resume formats and each one is ATS-friendly.
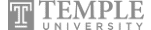
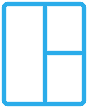
The chronological resume format
Also known as the “reverse chronological” resume, this is the most common type of format. You’re most likely already familiar with it.
As the name suggests, this format lists your most recent job first. Then your second-most recent job, your third-most recent job, etc…
Why do hiring managers like the chronological resume?
Hiring managers often prefer the chronological resume format for several reasons:
- It’s easy to follow – Recruiters can scan through your resume. It’s easy for them to find the companies you’ve worked for and the positions you’ve held.
- It’s the most traditional – Hiring managers are very familiar with this format. It won’t confuse them.
- It shows your career growth – Your work history makes it easy for recruiters to see how your career is going.
Who should use the chronological resume format?
Because this resume format focuses on work experience, it’s often used by job seekers who:
Have a strong work history
This format is ideal for job seekers who have lots of relevant work experience. It allows recruiters to see your career trajectory at a glance. They can get a good sense of the breadth and depth of your expertise.
Work in traditional industries
Many traditional industries prefer the chronological format. These industries include finance, engineering, healthcare, and legal professions. These sectors generally place a strong emphasis on a candidate’s work history.
Have a stable career path
The chronological resume is good at showing steady career growth within an industry. Hiring managers like to see this because it shows commitment.
How to set up a chronological resume
The reverse chronological resume contains the following sections, from top to bottom:
- Contact Information: Begin your resume with your name, phone number, and email address. You can also include a professional website or LinkedIn profile (if applicable).
- Resume Summary: This is a short statement about your goals, qualifications, and experience. It should provide a snapshot of your professional profile.
- Work Experience: This is the heart of the chronological resume. List your jobs in reverse chronological order, starting with your most recent position. Include the company name, job title, and dates of employment. Add a brief description of your responsibilities and accomplishments for each role.
- Education: This section should also be in reverse chronological order. List degrees earned, school names, and graduation dates. You may also want to list academic honors or certifications relevant to your field.
- Skills: This section allows you to highlight relevant skills. Include both hard and soft skills.
- Additional Sections: Depending on your background, you may choose to include more sections. These could include volunteer work, hobbies, publications, or foreign languages.
You don’t have to create your resume from scratch. You can use a resume template. This is a pre-designed layout that includes all the sections listed above. All you have to do is fill in your information.
Jobscan has free resume templates. Each one is ATS-friendly and can be easily customized to suit your needs.
Pros and cons of the chronological resume format
- Draws attention to employment gaps – Shows if you’ve had periods of unemployment or job breaks.
- Not ideal for career changers – Does not highlight your transferable skills. These are important if you are making a significant career change.
- Less focus on skills – Does not immediately highlight your specific skills. These are listed later in a separate skills section.
- Emphasizes career progression – Highlights promotions, increased responsibilities, and relevant experience.
- Preferred by recruiters – This makes it easy for them to assess your work history.
- Shows career stability – A stable career shows commitment to a job or industry.
- ATS-friendly – Applicant tracking systems are familiar with this format. They should have no problem reading and understanding your information.
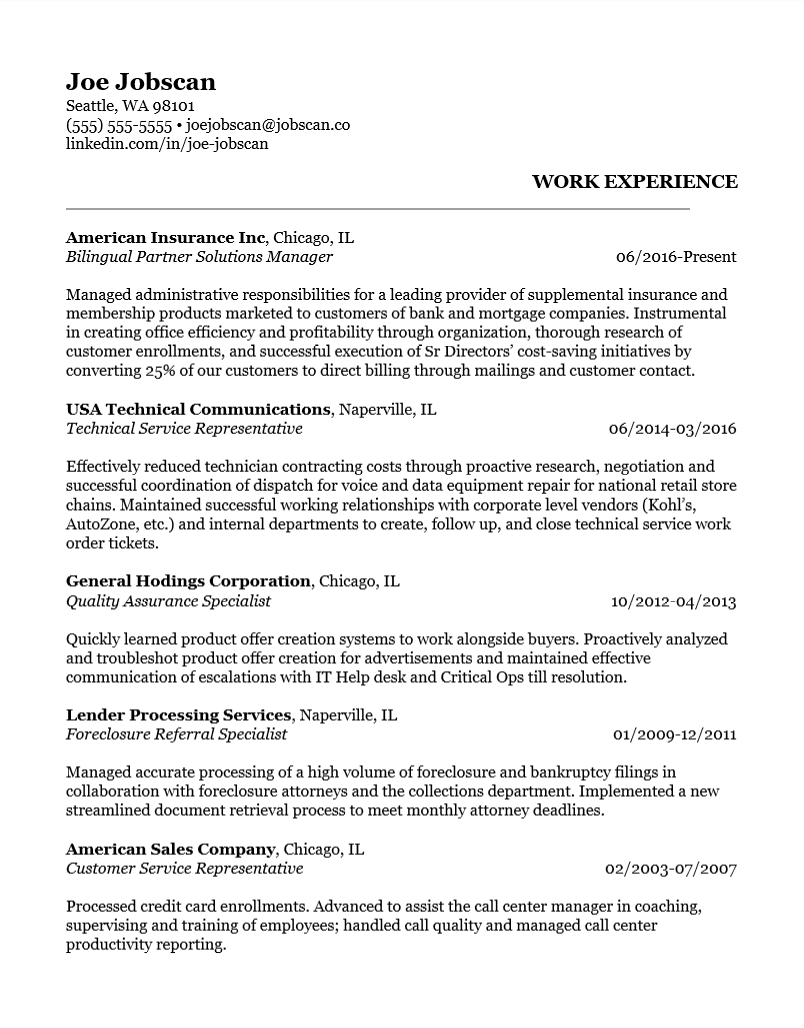
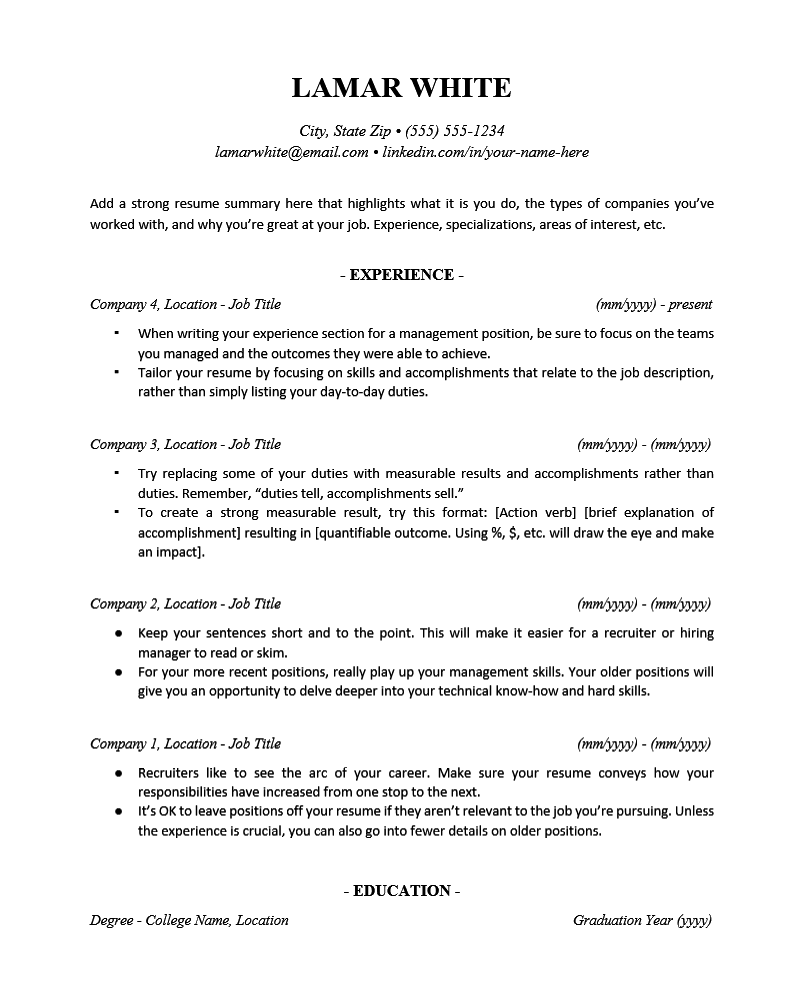
Functional resume format
This is also known as the skills-based resume format. It’s quite different from the chronological resume format.
The chronological format focuses on your work history. The functional format focuses on your skills and achievements. It minimizes your work experience.
This has several advantages:
- Focusing on your skills helps recruiters see if you can do the job.
- This format downplays negatives like employment gaps, career changes, and limited work experience. Instead, it focuses on positives, such as your transferable skills.
- This format also focuses on achievements that are relevant to the job you’re applying to. This makes it easier for recruiters to assess your capabilities.
Why do hiring managers like the functional format?
Actually, hiring managers don’t like the functional resume format!
This is because the lack of work experience makes it hard for them to understand your career. The functional format can also hide periods of unemployment. Hiring managers prefer transparency.
Another big reason why you shouldn’t use the functional resume format is that it’s not ATS-friendly.
ATS scan resumes for specific keywords, job titles, and dates. They use this information to assess an applicant’s qualifications for a specific job.
But functional resumes don’t focus on job titles and dates. So the ATS might have trouble reading and understanding them. As a result, functional resumes may not receive high rankings from an ATS.
Who should use the functional resume format?
While we don’t recommend using a functional resume, it can help certain job seekers. Especially those who:
Have transferable skills
Are you considering a career change? The functional format might be for you. It emphasizes your transferable skills that are relevant to the desired role.
Transferable skills are abilities that you can use in any job in any field or industry. They include things like communication, problem-solving, leadership, time management, organization, and adaptability.
Have limited work experience
The functional resume is for recent graduates or people with limited work experience. This is because it highlights things like your school achievements, hobbies, and volunteering.
Have employment gaps
The functional format downplays gaps in your work history. It redirects the focus of hiring managers toward your skills.
How to set up a functional resume
When creating a functional resume, follow this structure:
- Contact Information: This is the same regardless of which resume format you choose. Include your name, phone number, email address, and location.
- Resume Summary: The resume summary provides a concise snapshot of your qualifications. It should touch upon your unique skills, expertise, and accomplishments. The goal is to attract the reader’s interest.
- Skills Section: This is the heart of your functional (or skills-based) resume. This section should include a combination of hard skills (technical abilities specific to the job) and soft skills (transferable skills like communication, leadership, problem-solving, etc.).
- Use bullet points when creating your skills section. List your most relevant skills first. Whenever possible, try to include achievements that display relevant skills.
- Work Experience: Whatever work experience you have should come after your skills section. Don’t list detailed job descriptions. Instead, focus on the accomplishments, projects, and experiences that show your skills.
- Education: Include information about your educational background. This includes degrees earned, institution names, and graduation dates. Also include relevant coursework, certifications, or academic achievements.
- Additional Sections: Depending on your background, you may choose to include more sections. These could include volunteer work, hobbies, publications, or foreign languages.
If you don’t want to build your functional resume from scratch, try Jobscan’s free resume templates. They’re easy to customize and each one is ATS-friendly.
Pros and cons of the functional resume format
- Lack of detailed work history – Employers often want to see your work experience to see if you can do the job.
- No career timeline – Recruiters may find it hard to grasp the chronology of your work experience. This is because the focus is on your skills.
- Less suitable for established industries – Some industries focus more on work history.
- Highlights skills and achievements – This shows employers that you have what it takes to do the job.
- Good for career changers – This format focuses on your transferable skills. These give recruiters a good idea of your potential.
- Hides employment gaps – This format can lessen concerns about gaps in your work history.
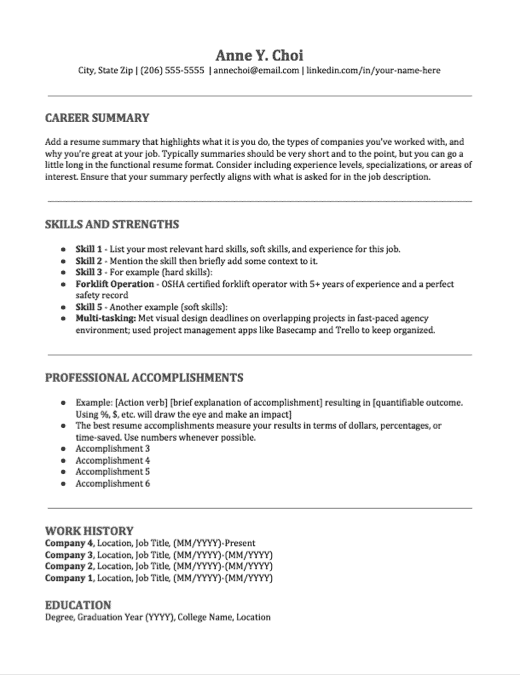
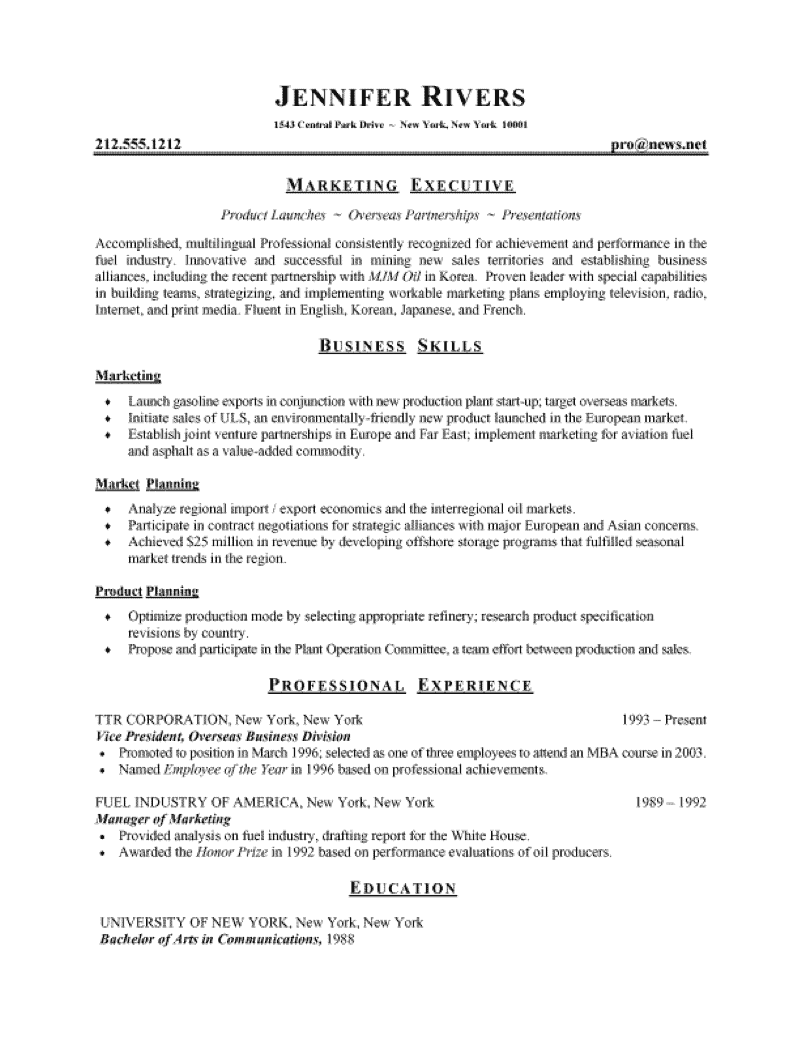
Hybrid resume format
The hybrid resume format is becoming more popular. It combines the best aspects of the chronological and functional resume formats.
That’s why it’s called a hybrid.
The hybrid resume emphasizes both skills and work history. It features a dedicated skills section at the top of the resume. Below that is a chronological work experience section.
This format is especially helpful when you have lots of work experience but also want to show off your skills and accomplishments.
Why do hiring managers like the hybrid format?
Hiring managers appreciate the hybrid resume format for several reasons:
- It strikes a balance – Recruiters can see your skills and your work experience.
- It focuses on key skills – Sometimes recruiters want to make sure you have the skills to do the job. This resume format tells them immediately.
- It shows career progression – The hybrid resume provides a clear overview of your career path.
Who should use the hybrid resume format?
Anyone can use the hybrid resume format to great advantage. It’s especially suited to job seekers who:
Have a diverse skill set
You might have the perfect skills for the job. But your work experience is a little weak. This format allows you to feature your skills while downplaying your work experience.
Want to emphasize achievements
The hybrid format allows you to showcase achievements as well as skills at the top of your resume.
Are changing careers
The hybrid is good if you are transitioning to a new field. It focuses more on your transferable skills and slightly less on your work history.
How to set up a hybrid resume
When creating a hybrid resume, follow this structure:
- Contact Information: Begin with your name, contact details, phone number, and email address. You can also include your professional website or LinkedIn profile (if applicable).
- Resume Summary: Try to distill your entire resume into a short, easy-to-read blurb. Summaries can help career changers who need a place to explain a shift in career trajectory.
- Skills Section: Use bullet points to list your skills and achievements. Include both hard skills and soft skills.
- Work Experience: List your jobs in reverse chronological order. Start with your most recent or current position. Include the company name, job title, and dates of employment. Also, include a brief description of your responsibilities and accomplishments for each role.
- Education: List your education as you would on a chronological resume. Include degrees earned, school names, and graduation dates. You may also want to list academic honors or certifications relevant to your field.
- Additional Sections: Depending on your background, you may choose to include more sections. These could include volunteer work, hobbies, publications, or foreign languages.
If you don’t want to build your hybrid resume from scratch, try Jobscan’s free resume templates. They’re easy to customize and each one is ATS-friendly.
Pros and cons of the hybrid resume format
- Can result in a longer resume – The hybrid format may result in a longer resume. This is due to the inclusion of both a skills section and a detailed work history. But this shouldn’t be a problem as long as your resume isn’t more than two pages.
- Requires more thought – It can be hard to achieve the right balance between skills and work history. It requires thoughtful consideration and planning.
- Highlights your skills – By showing your skills first, this format captures the attention of hiring managers who are looking for them.
- Showcases your career progression – This format includes a chronological work experience section. This gives employers a good sense of your professional background and experience.
- Adaptable – The hybrid resume is flexible and easy to customize for specific jobs.
- ATS-friendly – ATS should have no problem reading this type of resume format.
If you’re still not sure which format to use for your resume, follow this flowchart to help you decide based on your situation.
How to format your resume so an ATS can read it
It’s important to choose the right resume format. But it’s also important to optimize your resume layout and content for an ATS.
If your resume is not optimized for an ATS, it’s less likely to make it into the hands of a hiring manager. Even if you have relevant skills and experience.
Here are some tips for creating a resume that will get past the initial screening of an ATS.
- Use standard fonts – Stick to common fonts like Arial, Calibri, or Times New Roman. Avoid fancy or decorative fonts. The ATS may not recognize them.
- Keep it simple – Avoid excessive formattings, such as tables, images, or graphics, as they may confuse the ATS.
- Use simple headings – Use headings like “Work Experience,” “Education,” and “Skills”. The ATS can read these without a problem.
- Use plain text – Stick to basic formatting like bullet points and simple indentation. Avoid using headers or footers, text boxes, columns, or special characters.
- Use a font size that is easy to read – The recommended font size is 11-12 pt for regular text and 14-16 pt for section titles.
- Use the right margin – Make sure that the margins on all sides of your resume are 1 inch so that it doesn’t look too crowded.
- Include relevant keywords – Read the job description and pick out prominent keywords. Incorporate these keywords throughout your resume. This helps the ATS recognize your qualifications. It will then rank your resume higher in the search results.
- Use standard file formats – Save your resume as a .docx or .pdf file. These formats are widely compatible with most ATS systems.
- Avoid abbreviations and acronyms – Spell out acronyms and avoid excessive abbreviations. The ATS may not recognize uncommon abbreviations.
- Keep the file name simple – When saving your resume, use a simple file name. You could use the word “resume” for example. This makes it easier for the ATS and hiring managers to identify and organize your file.
Pro Tip: Use Jobscan’s free resume templates to start building your resume. All our templates are ATS-friendly and easy to customize.
5 tips for writing a resume that will get you interviews
Here are some additional tips that will help you create an effective resume:
Tailor each resume to the job you are applying for
Don’t make the mistake of sending out the exact same resume with every application. Yes, it’s easy. It’s also ineffective.
Instead, read the job description to find out which skills and qualifications are most important. Then try to include those skills on your resume.
When you use the same language on your resume that’s found in the job description, you increase your chances of getting an interview.
Highlight achievements as well as responsibilities
While it’s important to list your job responsibilities on your resume, you also want to highlight accomplishments.
Responsibilities are what you did. Accomplishments are how well you did it.
For example, if you increased sales or reduced costs, be sure to mention these accomplishments.
Use action verbs
Action verbs paint a clearer picture of your qualifications. They increase the overall impact of your resume.
Instead of simply stating that you were “responsible for” a certain task or project, explain how you took charge and made it happen.
For example, you could say that you “spearheaded a new initiative” or “coordinated a complex team effort.”
Use numbers
Try to use numbers whenever possible. Numbers show the true scope of your accomplishments to hiring managers.
Instead of saying that you “Created marketing campaigns” you could say that you “Created 10 successful marketing campaigns that generated a 20% increase in leads.”
Use active voice, not passive
Always try to use active voice instead of passive voice when writing your resume. Active voice is more direct, concise, and easier to read.
In active voice, the subject of the sentence is doing the verb. In passive voice, the subject is being acted upon by the verb.
If you’re not sure whether your resume is using active or passive voice, try running it through the Hemingway editor. It’s free and will tell you if you’re using passive voice.
Additional resume resources
Selecting the right resume format is the first step to creating an impactful resume. To learn more about how to create a resume that will stand out, check out these additional resources:
- How to Write a Resume That Recruiters Will Really Love – This step-by-step resume guide will teach you how to write a resume that stands out.
- How to Add Work Experience to Your Resume – Learn how to create a work experience section that will grab the attention of hiring managers.
- 8 Things You Need to Know About Applicant Tracking Systems (ATS) – Here’s everything you need to know about ATS. What they are, how they work, and especially how you can “beat” them!
- How to Write a Strong Resume Skills Section – Here are the top resume skills employers are looking for. Learn how to list them on your resume.
- Hard Skills vs. Soft Skills – Learn the difference between hard and soft skills and why you need both on your resume.
- Free Professional Resume Templates – These ATS-friendly resume templates feature sleek, minimalist designs.
FAQs about
resume formats
An ATS-friendly resume format is one that can be read by Applicant Tracking Systems (ATS). Employers use these systems to manage and filter large volumes of resumes.
When you use an ATS-friendly format, it increases the chances that a hiring manager will find your resume.
No, they are two different things.
Resume format refers to the structure and organization of the content in a resume. A resume template refers to a pre-designed layout you can use to create a resume.
There isn’t a specific “student resume format” per se. Students generally use the same resume formats as other job seekers. But they may emphasize different sections or information.
A student’s resume highlights coursework, internships, part-time jobs, extracurricular activities, and academic achievements.
The best resume format for you depends on your specific circumstances. This includes your work experience, career goals, and the industry you’re targeting.
Having said that, we like the hybrid resume format.
Employers are looking for job candidates who have the right skills. And the hybrid resume features skills right at the top of the resume. Employers also want to see a work experience section on a resume. The hybrid has that as well.
This powerful combination of skills and experiences makes the hybrid resume our top choice for 2023 and beyond.
Explore more resume resources